Security for video distribution environments, like operation or command centers, generally revolves around IT-based security protocols. This is typically because device access, control, and encryption of data travels across an organization’s network. As a result, the content itself isn’t always given the same level of scrutiny or security focus. To combat this security gap organizations should implement the CIA triad model – confidentiality, integrity, and availability. This model is a useful tool for data-heavy environments to establish appropriate controls and implement specific information security policies for content displayed on a video wall system.
Collaboration – How is Information shared?
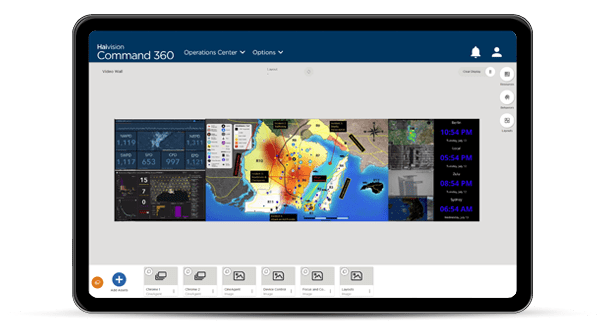
Operation and command centers use large video walls, comprised of several panels arranged together as a single display, for real-time situational awareness. The content displayed on these systems is not actually the underlying data, but rather rendered images of the data controlled by visual collaboration software like Haivision Command 360. This enables seamless integration with all system components such as video processors, encoders and decoders, permanently installed displays, or portable devices. The content sources can span multiple operational elements including, workstations, laptops, tablets, cameras, cable boxes, and more.How do organizations protect information?
To develop the appropriate security protocols around displayed content it helps to think of the content as a document. While the content is visible on screen it’s important to maintain the same information security best practices as if it were a printout of the information. The CIA triad includes three of the most fundamental and crucial cybersecurity needs. As organizations evaluate needs, use cases, and environment(s) for implementing a visual collaboration solution, the “triad” sparks focused questions about how these areas help to maintain security of critical visual content.Confidentiality – Who has access to content?
Maintaining confidentiality ensures that content displayed on the wall display is not accessible or visible to anyone who should not see it and often involves special training for those who need. Classification levels are a primary concern, especially for Department of Defense organizations. This is because content sources may originate from workstations across multiple classifications. The Bell–LaPadula Model (BLP) is used to enforce these principals in the three security properties below, also explained in our blog post Visual Content Security for Defense Organizations:- A display at a given security level may not display a source from a higher security level.
- A source at a given security level may not send video to a display at a lower security level.
- Discretionary access control (DAC) is maintained using an access matrix.
Integrity – Is content trustworthy?
Traditionally, integrity is thought of as protecting the data set so that it cannot be tampered with. However, for an operations or command center it must also be thought of as ensuring the correct content is displayed. In other words, to ensure information security best practices are in place. Individual content streams often lack the context of other content streams that are used to display critical information on a video wall. Security is not just about protecting the organization from malicious attacks. It also must protect the organization from human error that stems from good intentions. To address these scenarios user access controls and central administration is a must.Availability – Is content available when needed?
Video distribution systems should meet operations and command center availability requirements. It’s important that a system scale to fit as operational scope evolves, such as expansion from single to multi-site operations. In addition, backup capabilities can help mitigate data loss or connectivity interruptions. Visualization systems should also include an easy-to-use interface, properly maintained hardware, and 24/7 support in case an issue arises. Read about information security best practices, implementing multiple-classification operations centers with IP video distribution using the Bell–LaPadula Model, and more by downloading the Haivision MCS whitepaper Single-Site Multi-Enclave Distribution Best Practices.Introducing Haivision Command 360!
With more than a hundred new security features, built-in centralized administration, and Guardian Care 24/7 support, administrators easily maintain precise control over user permissions by defining the actions each role and group can access, and so much more. Schedule a free demo today.